Bitcoin enabled permissionless transfer.
Lightning enabled reciprocal transfer.
Cashu enabled blinded transfer.
#privatepayments

Tim Bouma
trbouma@getsafebox.app
npub1q6mc...x7d5
| Independent Self | Pug Lover | Published Author | #SovEng Alum | #Cashu OG | #OpenSats Grantee x 2| #Nosfabrica Prize Winner
It's rewarding to see the zaps come in, especially when I know that the payment trail goes cold as soon as it hits my system (save for the comment, which I forward on)
#nostr #safebox


After a very successful coding sprint, I am taking a few days to reflect on what I’ve built. This is the outcome of about a year’s worth of prototyping, coding and experimentation. I’ve proven that I can create a secure back-end communication channel between any two npubs to negotiate payments and records transfer.
The past few weeks were dedicated to integrating quantum-safe cryptography where I had to add in an additional protocol handshake to transfer the quantum-safe public key for key encapsulation and generating a shared secret to additionally encrypt the payload.
As you can see from the demo, the user actually sees nothing new, but I did add a message that indicates the quantum-safe key exchange has completed and the record is now safe for transmission.
In the end, it’s a layered approach. I use NIP-44/NIP-59 (symmetric encryption and gift-wrapping). I then further encrypt the encrypted payload using the quantum-safe shared secret. If an attacker manages to crack ECC with Shor’s Algorithm with a quantum computer, they’ll be rewarded with a a payload that is encrypted using the quantum-safe key exchange algorithms.
Is this overkill? You bet. But look at the video - the user won’t notice anything. This basically kills all quantum computer FUD and I honestly don’t believe there is a more secure way to do this in the world. Current ‘quantum-safe’ solutions being pitched, only protect the ‘pipe’ while everything that runs through it is in the clear, with the pipe being broken at each hop. I protect end-to-end the ‘payload’ - no reliance on pipes or friendly hops.
#nostr #safebox
Onward!
View quoted note →
Core capabilities of a globally available infrastructure that can’t be shut down by state or platform actors.
The capabilities to:
1. Communicate privately.
2. Settle without permission.
3. Verify without trusting.
The internet needs a new torso.
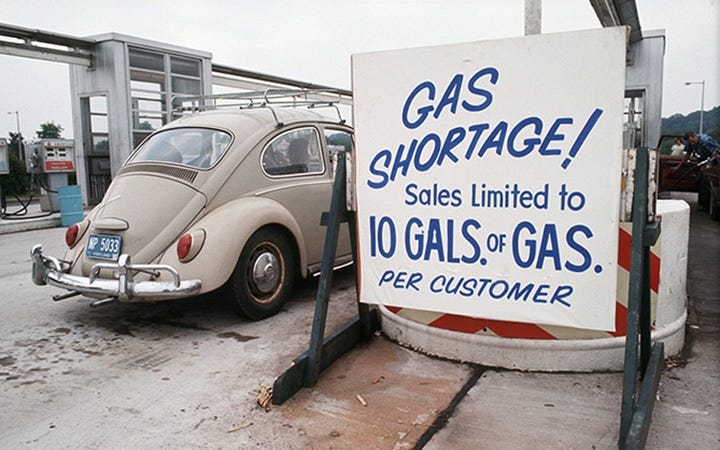
What it feels like after a hard and successful day.


This is a live demo showing one #safebox requesting a record from another #safebox. It looks straightforward- scanning a QR code but behind the scenes the safeboxes are negotiating which relays to use, transmitting quantum-safe public keys, additionally encrypting the payload and sending via encrypted gift wraps as ephemeral events that disappear in 10 minutes.
Nothing sensitive is transmitted using only TLS encryption or OAuth as I don't trust webpki certificate authorities and https.
What’s really cool is that I’ve landed on a pretty straightforward app coordination protocol.
1. Front-end web app presentation (HTTP GET/POST)
2. App dynamic interaction (Websockets)
3. Back-end data transfer (NIP-01, NIP-44, NIP-59 + PQC)
All sensitive data goes through the back end. TLS is not relied on for back-end security.
View quoted note →
It's been a heavy lift, but the past few weeks have been dedicated to making #nostr #safebox #quantumsafe.
For individual #safeboxes, they will have a separate encryption key that is never exposed via a public key. For transmission of records, payload are additionally encrypted using key encapsulation method (KEM).
Onward!


Good Afternoon.


Fastinating to see that government appointed amd unelected officials making statements that they are independent of the very governments they serve. 150 years ago, Walter Bagehot pointed this out contradiction of interests in his treatise on central banking, Lombard Street.
European Central Bank
International central bankers on the statement by Federal Reserve Chair Powell on 11 January 2026
The European Central Bank (ECB) is the central bank of the European Union countries which have adopted the euro. Our main task is to maintain price...

First attempt at post-quantum support for #nostr

GitHub
nips/PQ.md at pqc · trbouma/nips
Nostr Implementation Possibilities. Contribute to trbouma/nips development by creating an account on GitHub.
Hello pubpay world!