Does anyone know if someone from Fold is on here? I'm trying to order the debit card but they have an old address that has "null" in it, which is causing the app to crash when I go to edit the address. It's the "Everything looks good" screen where I verify the shipping address.
cc: @Marty Bent

josh
josh@westernbtc.com
npub1pc57...dmza
Loved by Jesus
nostr:nevent1qvzqqqqqqypzqr3falp286mfveqrarrpew975mtc2fa0tczktg465re38ml3g2hjqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qghwaehxw309aex2mrp0yh8qunfd4skctnwv46z7qpq7zajjjnzqkf4ag3pk3wj2v7p9nlpv3zaq4475rnjjrl696yh853qptp758
One of my favorite qualities of nostr: it works well with bad service.
You’re relying on a number of relays instead of 1 server, so chances are 1 or 2 of the relays are reachable.
This is especially noticeable with @Damus.
@n I’m trying the extension you’re using and I think I fixed the bugs 🤞. It’s my fault for recommending Gooti, it wasn’t in a place to be recommended. You can keep trying to nos2x-fox if you’re interested.
@Sam Hayes I've been running into an issue with Gooti that makes it unusable when trying to decrypt / encrypt messages: QuotaExceededError: storage.sync API call exceeded its quota limitations..
This error means the Gooti extension has hit Chrome’s (or the browser’s) `storage.sync` quota: the amount of data (or the rate of writes) that can be stored in the browser’s synced extension storage. When an extension tries to put too much into `storage.sync`—either in total size or too many updates in too short a time—it triggers this `QuotaExceededError`.
Why Does This Happen?
`chrome.storage.sync` (and equivalents on Firefox/Edge) has very tight size and write limits. This storage is meant to sync small extension settings across browsers, not large ephemeral data.
If Gooti is storing ephemeral encryption keys or large blocks of data on every decryption attempt, it can quickly exceed those limits.
Some extensions also run into trouble if they call `storage.sync` in a tight loop or rapid bursts.
How to Fix
Have Gooti store less data (or less frequently) in `storage.sync`.
If Gooti needs to store ephemeral keys, it should probably use `chrome.storage.local` (which has higher limits) or keep them in memory rather than `storage.sync`.
Clear out or reset the extension’s data.
If there’s an option in Gooti’s settings to “Clear cached data” or “Reset storage,” try that.
Check for a Gooti bug/upgrade
Sometimes the extension has a known issue where it writes too much or tries to store logs/keys in sync. Updating to the latest version might fix it.
Limit how many times you decrypt or how large the data is
If you’re calling Gooti’s decryption in a tight loop (e.g., hundreds of events in quick succession), you’re effectively spamming `storage.sync`. If possible, batch your calls or reduce the frequency.
Essentially, the error is an extension-level storage limitation rather than a problem with your code’s use of Nostr encryption. You or the extension’s developer need to ensure ephemeral secrets or larger data blocks aren’t pushed into the browser’s very limited `storage.sync`.
Will someone zap this note 16 sats? Promise to double it trust me bro.
Fireship is hard to beat, I linked to the part that made me think this. 😂
I wonder if, similar to a domain name service, we could have relays that only accept Outbox model kinds.
*asking an outbox only relay* "where do I find the relays this pubkey posts too?".
No more centralizing relays.
Google Chrome continues to push getting rid of ad blockers. Updated Chrome yesterday and it, again, disabled uBlockOrigin. They're stopping short of banning the extension because people would seek alternatives. I'm already there. What's your guys' preferred alternative browser?
@PABLOF7z mentioned that no one had bridged a lightning address to their nostr wallet, so I built it out.
Here's a demo of it working and verifying it with Olas. Now you can receive lightning payments to your LUD16 address and ecash sent directly to your nostr wallet. A wallet that travels with you all over nostr.
None of this would be possible without @calle, Pablo, and everybody else working tirelessly on nostr and cashu. Thank you guys.
This is still in early beta, so PLEASE be careful.
View quoted note →
Instead of mentioning Cashu - ecash is custodial every post, I think people will still get the idea if you mention it every other post.
Discouraging View quoted note →
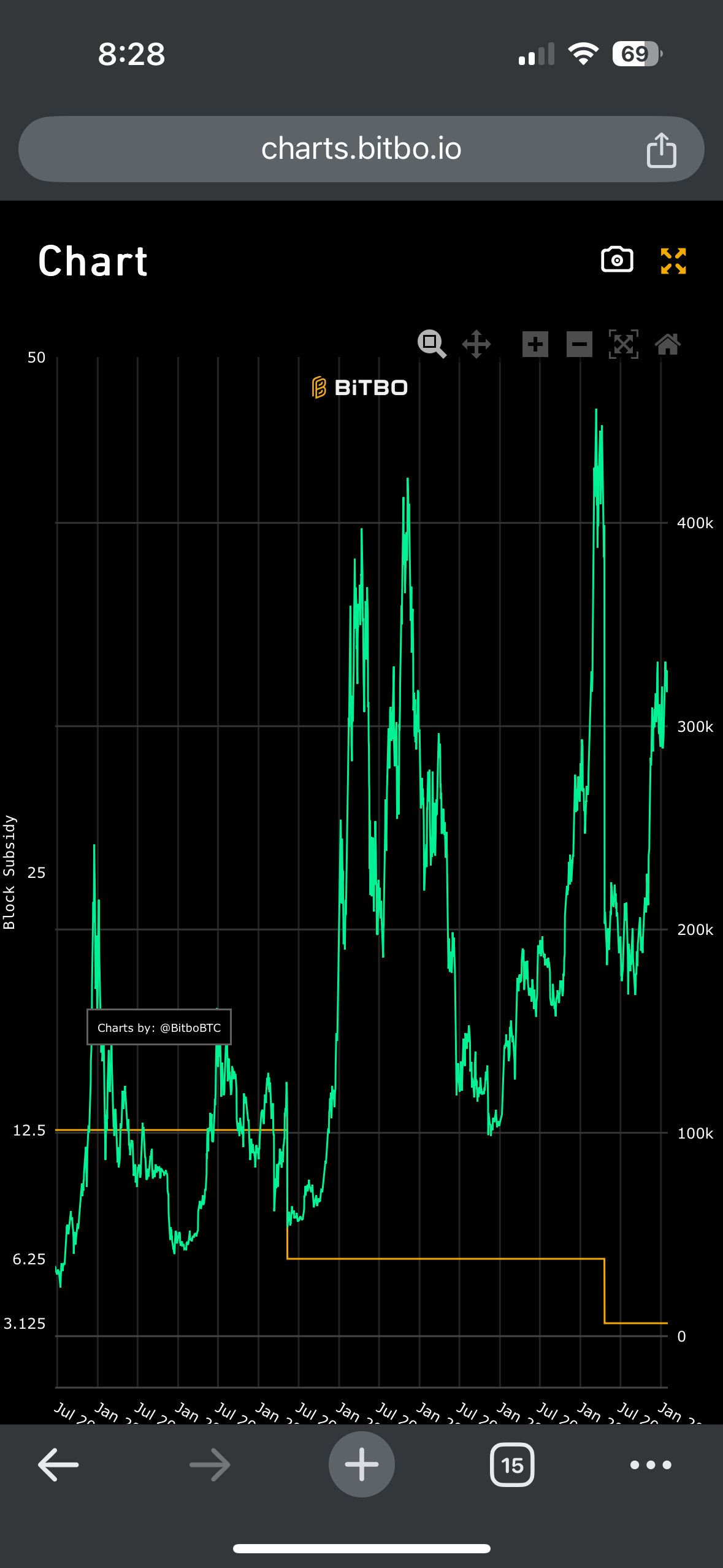
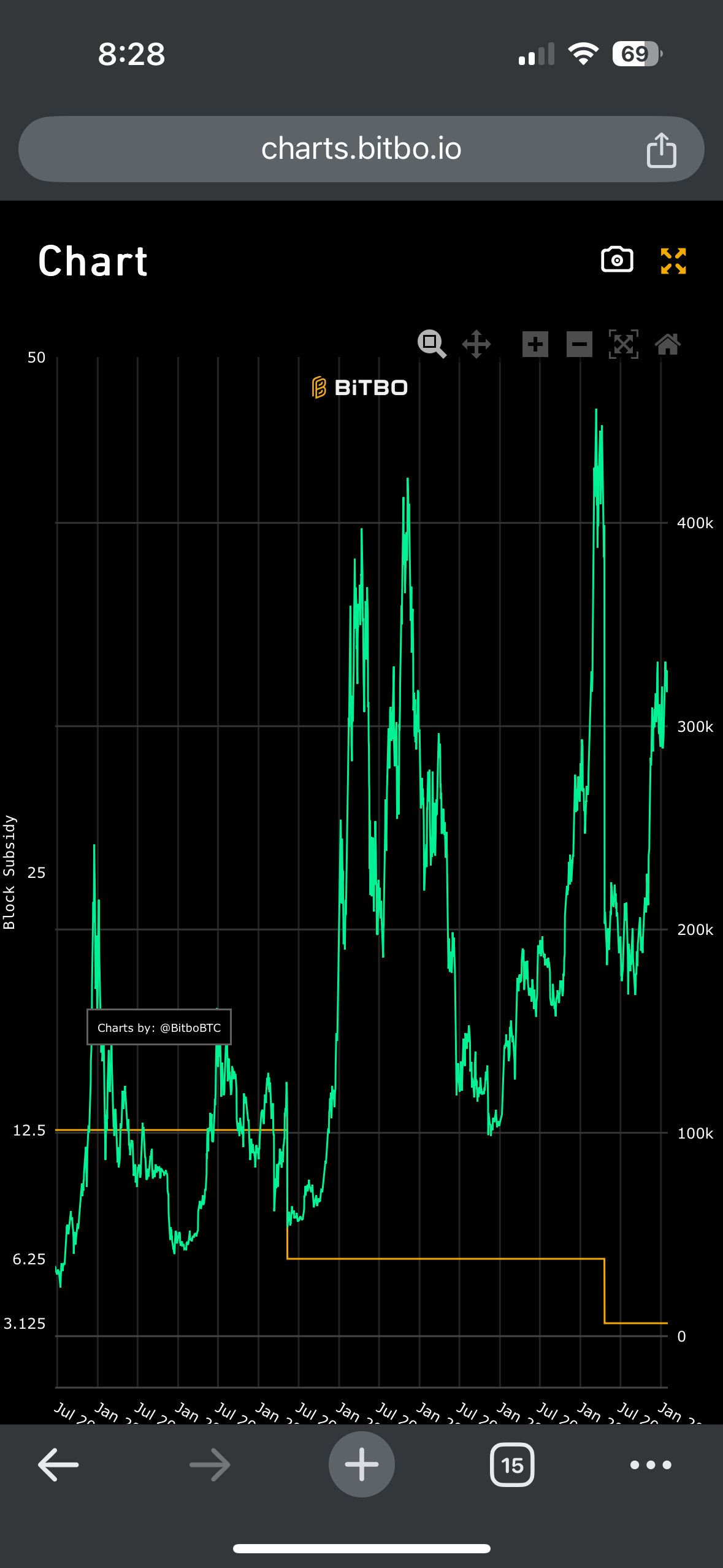
Never seen this chart before. Block subsidy reward in USD.
@fiatjaf @Vitor Pamplona NIP-17 obviously doesn't work with whitelisted relays because you have to create a random pubkey to send the message.
Could you instead, at some point (maybe when you first follow someone as it's a public event anyways), send a single encrypted message to the recipient intended for the transfer of a symmetric key? That way you could:
1. Encrypt a message using the symmetric key
2. Send it to the relay the pubkey is whitelisted on
3. The recipient's client, probably only checking for that event kind and narrowed to pubkeys they follow) would then attempt to decrypt it using the symmetric keys it's holding
4. The recipient's client would then store the message appropriately
@calle is there anything built into the wallet.cashu.me wallet where you can specify a receiving server and check for available "PAID" quotes locked to a specified P2PK? I'm not sure if there's a protocol for that or not. I know you're doing a hardcoded example with npub.cash. Maybe I can implement this feature if that's something you feel should be included. Thoughts?
If you're not already watching, get in here. This is a GREAT live stream with @jack and @ODELL .


zap.stream
ODELL is streaming
Nostr live streaming powered by Bitcoin lightning. Stream freely with Bitcoin payments, no censorship, open source.