#OPSEC365 054/365
Surveillance teams work in cycles: Stakeout, Pick-Up, Follow, Housing.
Understanding how pro foot monitoring operates is the foundation of detecting it. The team boxes the target in Stakeout. The trigger gives warning of movement. The Pick-Up establishes the follow. Housing is when the target stops. This cycle repeats all day.
To detect foot surveillance, vary your departure time and route. Surveillance teams stakeout from fixed trigger positions near your home or office - parked vehicles, cafe windows, bus shelters. Jenkins notes: operators get bored and co-locate.

Sam Bent
contact@sambent.com
npub1y7rv...d0r3
Agorist. Counter-economist. Privacy maximalist. Student of OPSEC. Anti-authoritarian. Free speech absolutist. Logician. Ex-Darknet Vendor. Youtuber.
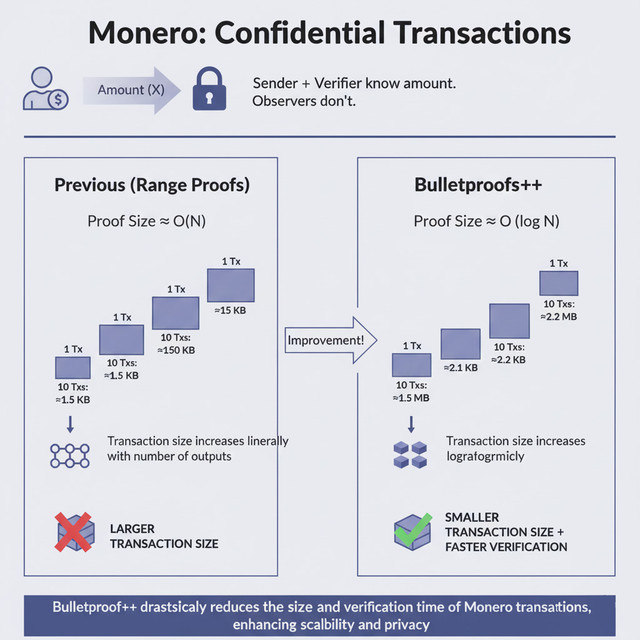
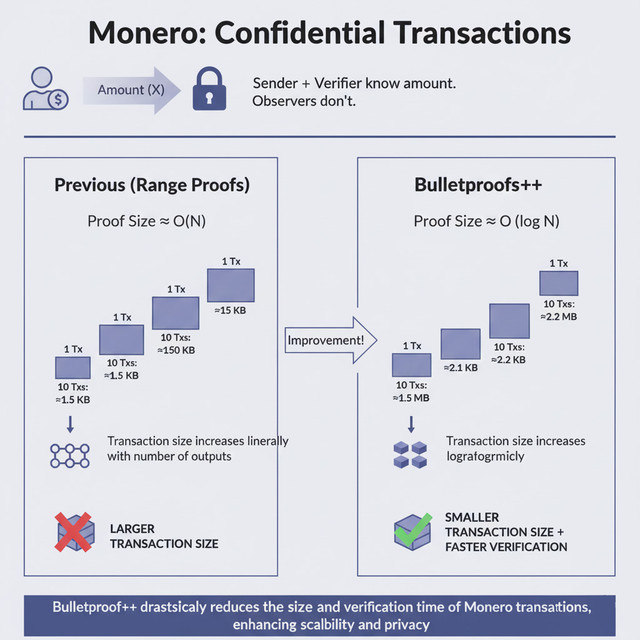
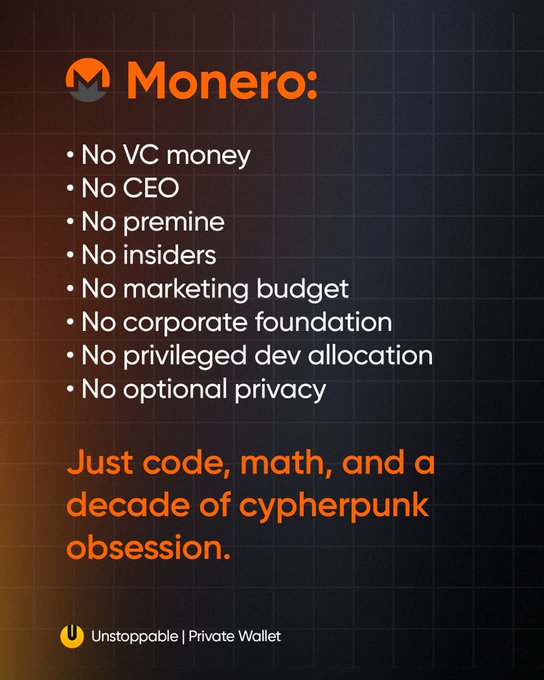
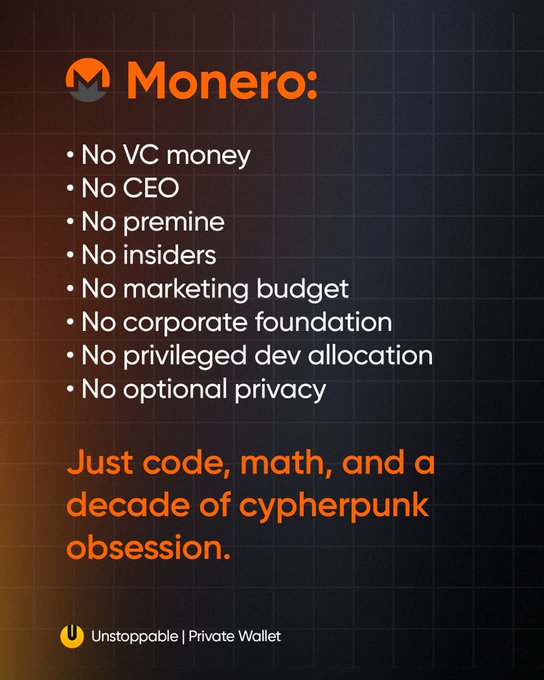
Every "Monero can't scale" argument from 2018 aged like milk after Bulletproofs++ went live.
#OPSEC365 052/365
Your email address reveals more than you think.
Firstname.lastname@company.com confirms your employer. A birth year in an address tells your age. College emails persist in breach databases long after graduation. HaveIBeenPwned indexes over 14 billion breached accounts—your old address is almost certainly in one.
An email address is a key. Most people hand out copies to anyone who asks.
Compartmentalize by purpose: professional email for work, a separate address for accounts you don't trust, and a private address only trusted contacts know. SimpleLogin and AnonAddy generate per-service aliases (e.g., amazon@yourdomain.anonaddy.me) forward to your real inbox.
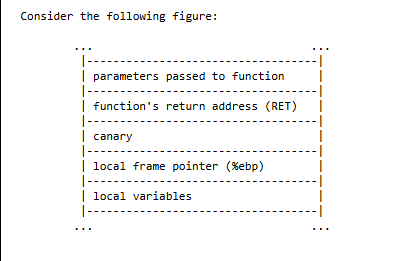
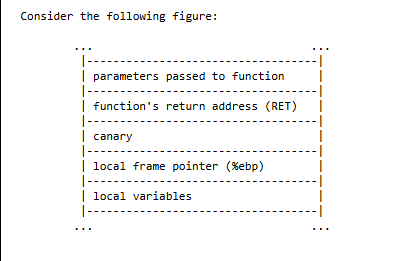
Return-to-libc attacks when stack protection made shellcode harder.
"Return-to-libc attacks allow code execution without injecting any code onto the stack."
- 𝗕𝘆𝗽𝗮𝘀𝘀𝗶𝗻𝗴 𝗦𝘁𝗮𝗰𝗸𝗚𝘂𝗮𝗿𝗱 𝗮𝗻𝗱 𝗦𝘁𝗮𝗰𝗸𝗦𝗵𝗶𝗲𝗹𝗱 by Bulba and Kil3r (2000)


Phrack
Bypassing StackGuard and StackShield
Click to read the article on phrack
#OPSEC365 051/365
Voter registration records are public in most states.
Your full name, home address, party affiliation, and voting history are available to political campaigns, researchers, journalists, and data brokers. Some states publish this online for free. Others sell it in bulk.
Voter registration data is public record in most states. Name, address, party, and voting history — available to campaigns, researchers, and anyone else who asks.
Some states let you request confidentiality if you have a noted threat, but most don't. Address Confidentiality Programs exist for survivors of domestic violence. For everyone else, the best you can do is use a PO Box where allowed and know your registration is public regardless.
HSBC's own ad copy explains exactly why Monero needs to exist
when someone controls your finances, they control you, and the only money that can't be controlled, frozen, or surveilled is the money they're trying to ban.


#OPSEC365 047/365
Your smart TV shares a network with your laptop, phone, and NAS. That's a compartmentalization failure.
ACR runs by default on Vizio, Samsung, and LG — fingerprinting your viewing. A TV with a vulnerable update path is a lateral pivot into your LAN.
Cronk's SEPARATE strategy: partition contexts with different trust levels. Your TV needs internet. It has no need to see your other devices.
VLAN your IoT tier. Your TV doesn't need to know your NAS exists.
Implementation: create an isolated IoT VLAN with internet-only egress, no routing to your primary LAN. A smart TV's legitimate function requires only outbound streaming access — zero visibility into personal devices.
Secure means your funds can't be seized without your keys,
private means no one sees your balance or transactions,
untraceable means chain analysis is useless,
Monero is the only cryptocurrency that delivers all three by default.


Monero devs spent years quietly building FCMP++
while Zcash devs spent years lobbying regulators and tweeting about compliance
one project shipped privacy,
the other shipped press releases.


Happy birthday to the only 12-year-old the FBI, IRS, Chainalysis, and Europol
all failed to groom into an informant.
$XMR


#OPSEC365 021/365
OPSEC Step 2 is threat analysis: research your adversary's actual collection capabilities. Public records, court databases, social media aggregators, data brokers, and reverse image search form a surveillance infrastructure anyone can access for under $50/month.
Your adversary doesn't need hacking skills. They need patience.
NTTP 3-13.3 lists adversary collection as HUMINT, SIGINT, OSINT, GEOINT, and MASINT. For most civilians, HUMINT and OSINT are the primary threats. Digital countermeasures alone fail if your adversary collects via human contact.
Ken Thompson's acceptance speech for the Turing Award on security thinking.
"The moral is obvious. You can't trust code that you did not totally create yourself."
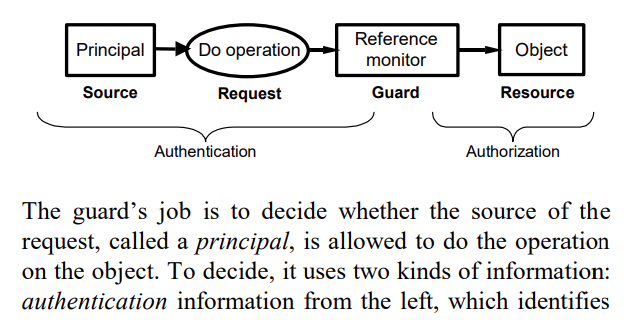
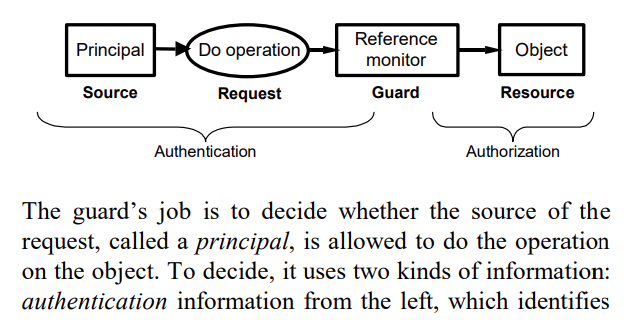
- 𝗖𝗼𝗺𝗽𝘂𝘁𝗲𝗿 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗶𝗻 𝘁𝗵𝗲 𝗥𝗲𝗮𝗹 𝗪𝗼𝗿𝗹𝗱 by Butler Lampson (2004)
https://www.microsoft.com/en-us/research/wp-content/uploads/2004/06/Computer-Security-in-the-Real-World.pdf
Monero has survived ten years on donations and volunteer labor while VC-backed "privacy" projects burned through millions building compliance tools,
turns out you don't need a marketing budget when the product actually works.
Congress forced telecoms to build surveillance backdoors in 1994.
Chinese hackers found them.
The government's response is to ban your router.

