#OPSEC365 076/365
Browser extensions execute across all tabs and contexts — bank, medical, work — simultaneously.
MITRE Pre-ATT&CK PRE-T1119: adversaries build digital footprints across platforms to establish credible personas. A malicious extension does the inverse with one install.
Cronk's HIDE/Restrict: enforce access controls limiting visibility. 'Read all data on all sites' bypasses every logical compartment.
Separate browser profiles per identity. Extensions don't cross profiles.
Create distinct browser profiles per context: work, personal, research, anonymous. Extensions installed in one profile are invisible to another. Never grant broad cross-site permissions inside your primary identity profile — the permission scope defeats compartmentalization.

Sam Bent
contact@sambent.com
npub1y7rv...d0r3
Agorist. Counter-economist. Privacy maximalist. Student of OPSEC. Anti-authoritarian. Free speech absolutist. Logician. Ex-Darknet Vendor. Youtuber.
Members of Congress have private gold elevators, private gyms, dining rooms, they exempt themselves from laws and have a lifetime pension after one term.
The people who fund all of it have to abide by an uncountable amount of laws (google it), pay late fees, get pulled over for going 5 mph over the speed limit.


#OPSEC365 075/365
Warranty registrations ask for data they don't need.
When you register a product for warranty, they ask for name, address, email, phone, purchase date, sometimes even income range. This data goes to marketing databases, not just warranty files. The warranty itself usually just requires proof of purchase.
The warranty doesn't require registration. The registration form exists to collect your data.
Most warranties are valid whether you register or not if you keep your receipt. If you do register, use minimal accurate information and skip optional fields. A separate email address for product registrations keeps spam and data collection segregated from your primary inbox.
Same agency that ran COINTELPRO now begs for financial surveillance access, and Monero keeps saying no.


#OPSEC365 074/365
When you sell a home, real estate photos live online forever.
Interior layouts, security system placements, window positions, landscaping details. Zillow, Redfin, and Realtor.com cache these images indefinitely. Future occupants might not appreciate having their floor plan public, and you might still appear in photos.
Zillow and Redfin cache listing photos indefinitely. The interior of a home you sold years ago is still publicly browsable.
Some sites honor removal requests, others don't. When selling, consider what interior details those photos reveal to burglars. After moving, check if your face or possessions appear in previous listing photos.
You work 3 months out of the year for the government.
It's not a choice.
If you think that money goes towards the roads and shit, you're wrong.
They will kill or imprison you if you refuse.
I rob you and buy you a 5 dollar sandwich from the 30,000 I stole,
this is the logic.
#OPSEC365 073/365
Shared family streaming accounts are a compartmentalization failure disguised as savings.
Every profile feeds one behavioral model. Viewing patterns across all users collapse into one household record — one subpoena retrieves everything.
The Privacy Spectrum (Polyonymy): distinct identities prevent cross-contamination. Shared accounts dissolve that.
Separate accounts per person keeps each person's behavioral record independently non-attributable.
Each household member should operate under distinct credentials with no shared payment linkage where avoidable. Viewing behavior, search history, and content preferences aggregated across persons creates a richer combined profile than either alone.
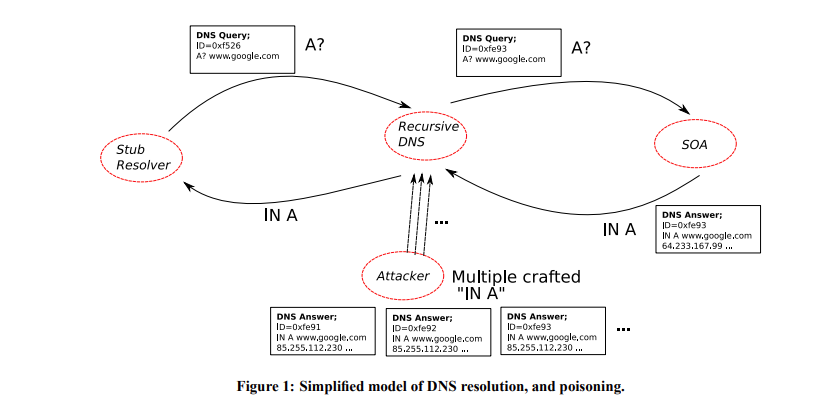
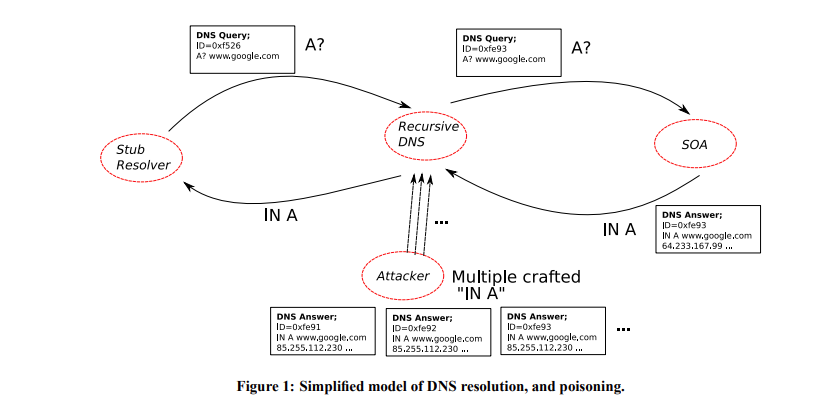
DNS cache poisoning attacks and DNSSEC weaknesses.
"The DNS infrastructure is vulnerable to cache poisoning attacks that can redirect users to malicious sites."
- 𝗜𝗻𝗰𝗿𝗲𝗮𝘀𝗲𝗱 𝗗𝗡𝗦 𝗙𝗼𝗿𝗴𝗲𝗿𝘆 𝗥𝗲𝘀𝗶𝘀𝘁𝗮𝗻𝗰𝗲 𝗧𝗵𝗿𝗼𝘂𝗴𝗵 𝟬𝘅𝟮𝟬-𝗕𝗶𝘁 𝗘𝗻𝗰𝗼𝗱𝗶𝗻𝗴 by David Dagon et al. (2008)
https://astrolavos.gatech.edu/articles/increased_dns_resistance.pdf
#OPSEC365 072/365
A skilled investigator doesn't start with you. They start with a name and a zip code.
In the first 30 minutes: ThatsThem links your name to a phone number. That number pulls your address history from Whitepages. Your county clerk has your voter registration with your exact address. PACER surfaces any federal court involvement. Google indexes you across everything.
You've been profiled before they've spent a dollar.
The first 30 minutes of OSINT on anyone uses entirely free, publicly indexed sources. Voter registration is searchable by name in most U.S. counties. Court records are public. Data brokers aggregate all of it. The investigator isn't hacking anything.
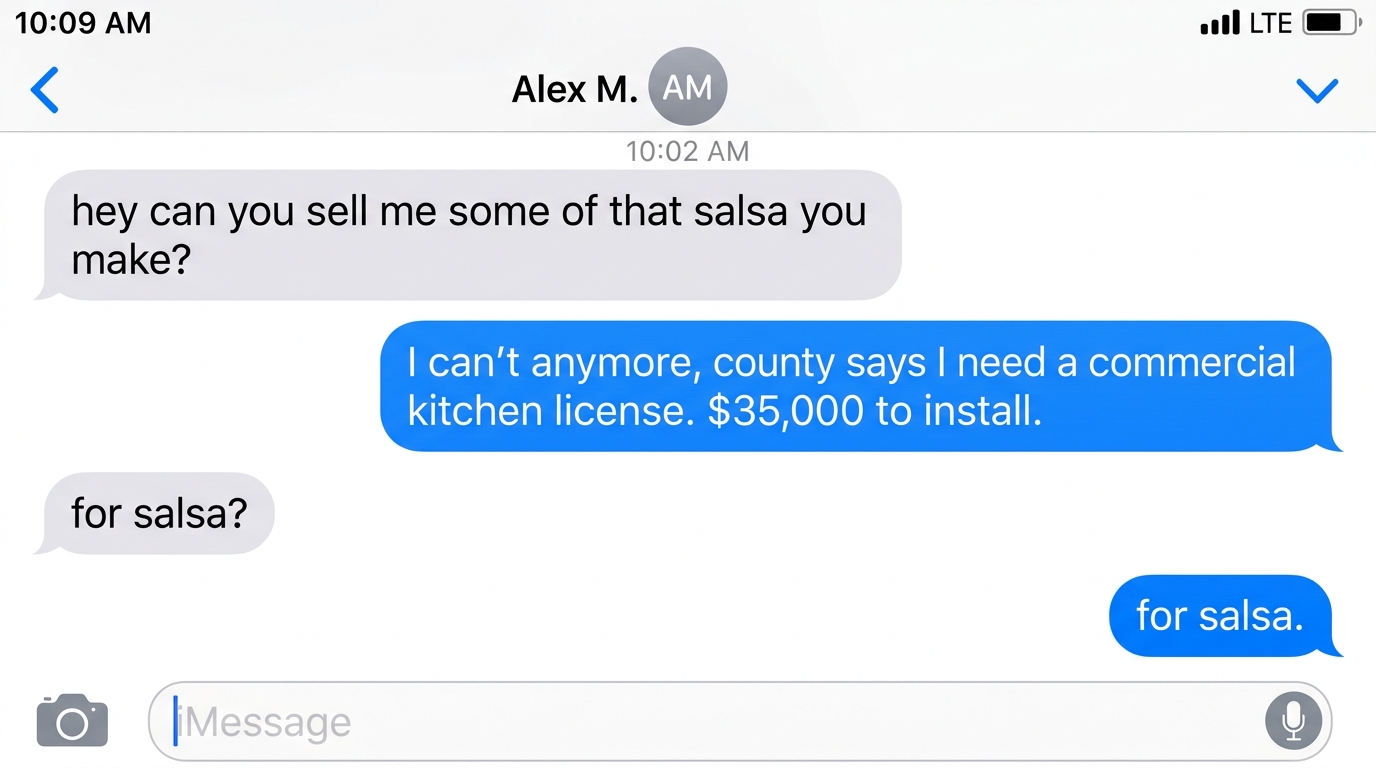
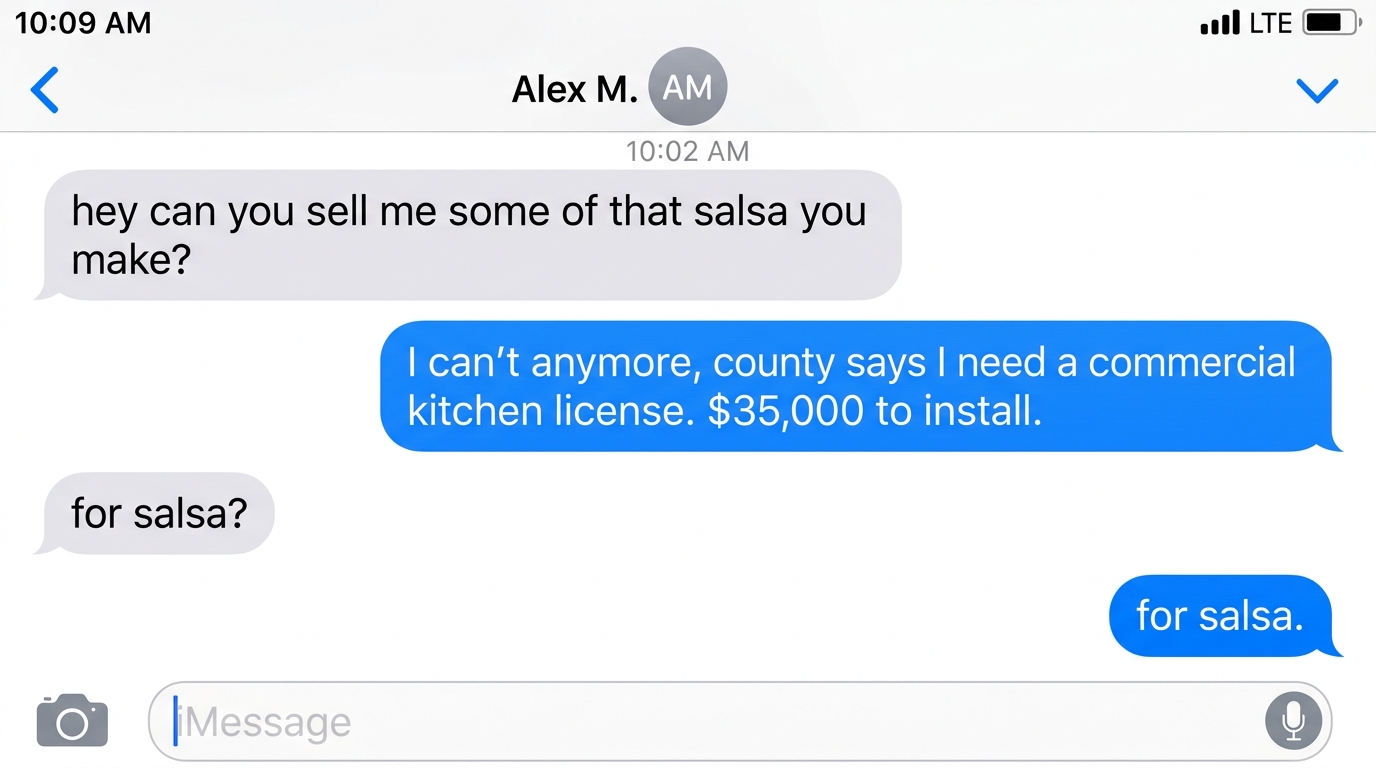
The government will let corporations pump high fructose corn syrup into everything on the shelf, despite heart disease being the #1 killer in America. But you need $35,000 in permits to sell homemade salsa to your neighbor, because you never paid off Congress with lobbyists.
#OPSEC365 071/365
Thermal receipt paper fades, but the transaction record doesn't.
That receipt you kept for warranty purposes will be blank in a few years. Meanwhile, the merchant, the payment processor, and the bank all have permanent records of what you bought, when, and where. The paper is ephemeral, but the data isn't.
Stop relying on receipts for records and consider what permanent transaction logs exist about you.
If you need receipts for warranties or returns, photograph them immediately before they fade. For privacy purposes, understand that keeping or discarding receipts doesn't affect the digital records that exist. Cash purchases at stores without cameras create the fewest records.
Anyone with an internet connection can search your Bitcoin balance, trace your transaction history, and link it to your identity
but tell me again how "number go up" makes that a feature and not a catastrophic design flaw.


#OPSEC365 070/365
Most color printers embed invisible tracking codes on every page.
These machine identification codes, also called printer dots, encode the printer's serial number and timestamp on every printout in a pattern invisible to the naked eye. The NSA leaker Reality Winner was caught partly because of these dots.
If you're printing something sensitive, know that the printout itself may identify the printer used.
Black and white laser printers generally don't include these dots. If you must print anonymously, use a printer you don't own, purchased with cash, from a public location. The EFF maintains a list of printers known to embed tracking codes.
#OPSEC365 069/365
Gym access logs track when you work out down to the minute.
Card scans at entry and exit, equipment check-ins, class registrations. If your gym sells data or gets breached, your fitness schedule becomes part of your public profile. Combined with other data, this reveals when you're not home.
Your gym knows when you're not home. So does whoever buys their data.
Some gyms sell aggregated data to brokers. Others have been breached repeatedly. If your gym requires a membership card, you're logged every time. Vary your schedule occasionally, or choose gyms with less surveillance.
#OPSEC365 068/365
Pet microchips and registrations link animals to owners.
When you chip your pet, that database entry contains your name, address, and contact info. Pet licensing, vet records, and adoption paperwork all create associations. Someone looking for you could find you through your pet.
Your pet's microchip database entry contains your name, address, and phone number. Someone looking for you could find you through your dog.
If you've moved and haven't updated your microchip registration, do it now. Consider whether the address on file needs to be your home or whether a PO Box works. For high-threat individuals, this is another vector that often gets overlooked when hardening other areas.
FCMP++ turns the entire Monero blockchain into your anonymity set instead of just 16 decoys.


#OPSEC365 067/365
Your work laptop and phone are not private.
Employers can legally monitor everything you do on company devices. Keyloggers, screen captures, email scanning, browser history, location tracking. That personal message you sent, that job listing you looked at, that side project you worked on during lunch. IT can see all of it.
Treat any company-owned device as if your boss is watching over your shoulder.
Keep personal and work activities on separate devices. Don't use work email or slack for personal conversations. Don't browse personal sites on work networks. Some employers are transparent about monitoring policies, others aren't. Assume the worst and act accordingly.
#OPSEC365 066/365
Medical records contain your most sensitive information.
Diagnoses, medications, mental health treatment, substance abuse history, sexual health data. HIPAA limits who can access this without consent, but breaches happen constantly. Hospital systems, insurance companies, and medical devices all store and transmit this data.
Patient portals log every provider who accessed your records. Unauthorized access by hospital employees has been documented at every major health system.
Most patient portals show access logs. Review yours to see which providers and staff have viewed your records. You have the right to request an accounting of disclosures from healthcare providers. Ask for it and see where your information has traveled.
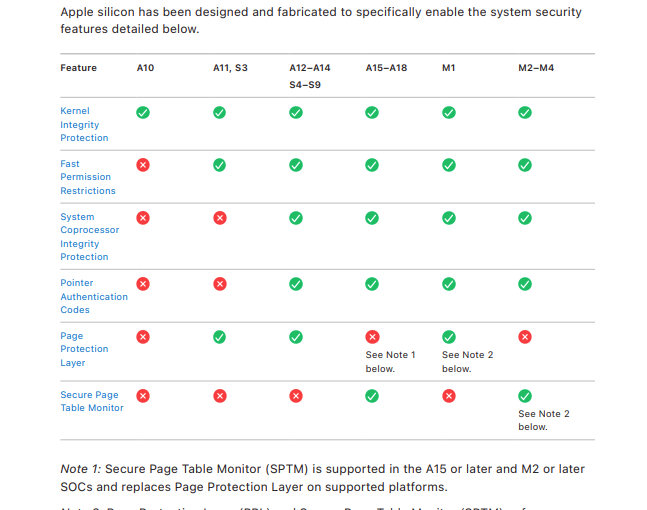
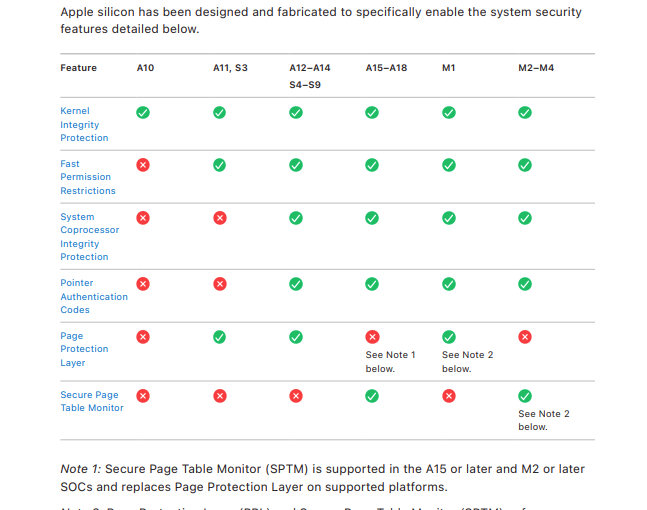
iOS security model and jailbreaking research.
"iOS implements multiple layers of security to protect user data and system integrity."
iOS Security White Paper by Apple (multiple editions)
https://help.apple.com/pdf/security/en_US/apple-platform-security-guide.pdf
#OPSEC365 065/365
Your social security number appears in more places than you'd expect.
Medical records, insurance claims, employment files, credit applications, tax forms, student loans. Every organization that has your SSN becomes a potential leak point. It only takes one breach for your number to end up in criminal databases.
Your SSN was issued once. The number of organizations holding it has grown every year since.
You can ask orgs to remove your SSN from records if they no longer need it for business purposes. Some will comply, others won't. Credit freezes at all three bureaus prevent new accounts from being opened, limits the damage if your number is exposed.