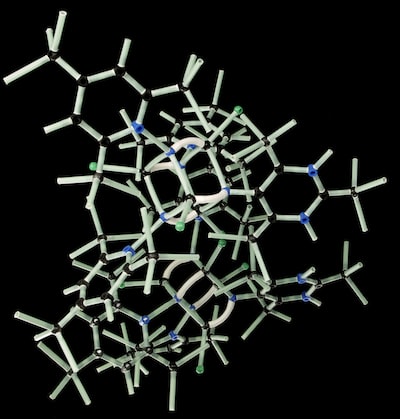
#Amazon's #AWS SSM agent can be used as post-exploitation RAT #malware
Abusing the SSM agent allows attackers to breach AWS accounts to execute commands remotely without being detected, as the traffic looks like regular activity generated by the agents.
 #ethicalhacking #infosec #cybersecurity #nostr
#ethicalhacking #infosec #cybersecurity #nostr

BleepingComputer
Amazon's AWS SSM agent can be used as post-exploitation RAT malware
Researchers have discovered a new post-exploitation technique in Amazon Web Services (AWS) that allows hackers to use the platform's System Ma...

 Now let's make the same question but with a misspelling marked as red
😂😂😂😂
#funny #nostr
Now let's make the same question but with a misspelling marked as red
😂😂😂😂
#funny #nostr



 #ethicalhacking #infosec #cybersecurity #nostr
#ethicalhacking #infosec #cybersecurity #nostr