Pretext vs DOM Reflow: Real Benchmarks for Streaming AI Interfaces
https://paragraph.com/@metaend/pretext-vs-dom-reflow-streaming-benchmarks
#Research #frontend #dev #llm

ngmi
ngmi@zaps.lol
npub14p7f...dzry
Contact https://meta.orbiter.website/
MiniMax Music 2.6 is now available! Generate complete songs from prompts plus structured lyrics, choose your bitrate and sample rate, and enable instrumental-only mode when you want no vocals.
 #ai #llm #minimax
#ai #llm #minimax
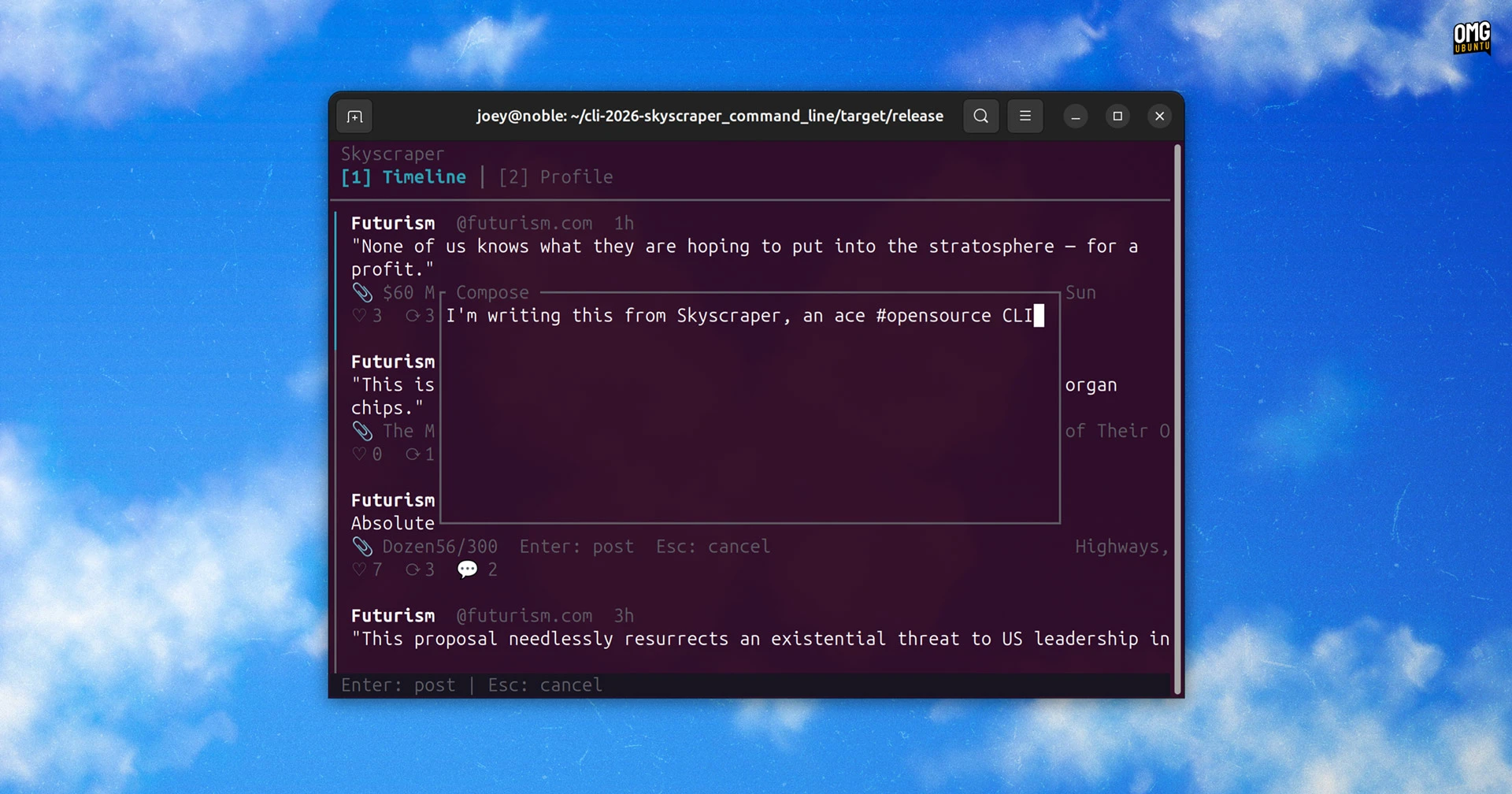
Join NanoGPT
Create your NanoGPT account and get access to leading AI models for chat, coding, images, and video.
"US President Donald Trump also endorsed Orban ahead of the Sunday polls." Everything this guy can't manipulate himself ends up in a total disaster
Flatpak-style launcher for sandboxed WebAssembly tools. Single binary, local-first, no accounts, no telemetry.
Built for agents and humans alike — every tool ships with a machine-readable skill file so agents can discover, understand, and invoke tools without guessing.


Tangled
metaend.eth.xyz/wasmbox-cli
Flatpak-style launcher for sandboxed WebAssembly tools. Install, verify, and run .wasm binaries with explicit capability grants. Single binary, loc...

My AI frame for important shit: Legal, NDA, critical emails go through my claude first, as it has the most complete knowledge of my activities. BUT then I also send Claude's answer through an open source LLM, to get a second opinion. More often than not there are little details missing or coming up. Rn I use Minimax M2.7 via nano
Join NanoGPT
Create your NanoGPT account and get access to leading AI models for chat, coding, images, and video.
Trump left humiliated as CNN breaks bombshell news on Iran ceasefire — and it’s very bad news for the president


The Daily Sight
Trump left humiliated as CNN breaks bombshell news on Iran ceasefire — and it's very bad news for the president
CNN cut into its regular programming on Tuesday evening to deliver urgent breaking news that stopped the country in its tracks. The US-Iran conflic...
Lmao View quoted note →
Iran shuts Strait of Hormuz in retaliation for Israeli strikes on Hezbollah
Deliberately targeting civilian infrastructure like power plants and bridges is widely considered a violation of international humanitarian law. The key provisions:
Protocol I of the Geneva Conventions (Articles 52-54) prohibits attacks on objects indispensable to the civilian population and requires distinction between military and civilian targets. Power grids and bridges serving civilian populations are protected.
The Rome Statute of the ICC classifies intentionally directing attacks against civilian objects as a war crime.
Disgruntled researcher leaks “BlueHammer” Windows zero-day exploit
BleepingComputer
Disgruntled researcher leaks “BlueHammer” Windows zero-day exploit
Exploit code has been released for an unpatched Windows privilege escalation flaw reported privately to Microsoft, allowing attackers to gain SYSTE...
Wasmbox 0.3.2 released
network - Per-host outbound HTTPS via WASI HTTP. Host-filtered: tools can only reach hosts declared in their manifest. All other requests are rejected at the runtime level.
Cool tools coming!
 #wasm #ai #wasmbox #a2h #agents
#wasm #ai #wasmbox #a2h #agents
Tangled
metaend.eth.xyz/wasmbox-cli
Flatpak-style launcher for sandboxed WebAssembly tools. Install, verify, and run .wasm binaries with explicit capability grants. Single binary, loc...
Every proof-of-humanity system today works the same way: the platform verifies the user.
But when AI agents are the ones executing decisions, that model breaks. The agent has a session token, not proof of a pulse.
I'm proposing a new primitive: A2H Proof (Agent-to-Human Proof).
Instead of platforms checking users at signup, the agent itself challenges the human at the decision boundary. The human responds with a cryptographic proof. The agent verifies it in a sandboxed runtime. No intermediary.
Why this matters now: EU AI Act Article 14 requires meaningful human oversight for high-risk AI systems. "Meaningful" is the key word. A login cookie from this morning doesn't qualify.
A2H places verification where it actually matters -- the exact moment an AI system is about to act.
Full writeup: https://paragraph.com/@metaend/a2h-proof
#AI #ProofOfHumanity #EUAIAct #AgentInfrastructure #WasmBox
Proton Meet Isn't What They Told You It Was
 Hilarious
Hilarious

Sam Bent
Proton Meet Isn't What They Told You It Was
Proton built Proton Meet to escape the CLOUD Act. They built it on CLOUD Act infrastructure. Their website promises "not even government agencies" ...
Gemma 4 31B TEE is now available! It runs Google's #Gemma 4 31B inside a Trusted Execution Environment with provider attestation support, so your prompts and outputs stay private even from the inference host. It supports structured output and a 256K context window.
Join NanoGPT
Create your NanoGPT account and get access to leading AI models for chat, coding, images, and video.
Containers share a kernel. That's a trust assumption.
WASM starts with zero capabilities. That's a trust guarantee.
We shipped 9 tools inside this model. Agents use them daily. The sandbox enforces what they can touch. The manifest is the attack surface.
August 2 is less than 120 days away.
curl -sSf https://tangled.org/metaend.eth.xyz/wasmbox-cli/raw/main/install.sh | sh
Announcing 1-bit Bonsai: The First Commercially Viable 1-bit LLMs
.png)
.png)
PrismML — Announcing 1-bit Bonsai: The First Commercially Viable 1-bit LLMs
Your code review agent reads a 2,000-line unified diff to figure out what changed.
It burns 8,000 tokens parsing plus signs and minus signs. Then it tells you: "3 files were modified, mainly in the request handler."
That answer was 12 tokens. The other 7,988 were waste.
We built diffsummary. Pipe any git diff in. Get structured JSON out.
git diff HEAD~1 | wasmbox run diffsummary
{
"files_changed": 3,
"insertions": 47,
"deletions": 12,
"files": [
{
"path": "src/main.rs",
"status": "modified",
"insertions": 30,
"deletions": 8,
"functions_touched": ["handle_request", "validate_input"],
"hunks": [{"start_line": 42, "summary": "+22/-5 lines in handle_request"}]
}
]
}
The agent now knows which files changed, which functions were touched, and how many lines per hunk. Without reading a single + or - line.
This is how token-efficient code review works:
# Step 1: What changed? (structured, not raw)
git diff HEAD~1 | wasmbox run diffsummary -- --files
modified src/main.rs +30/-8
added src/auth.rs +15/-0
modified wasmbox.toml +2/-1
# Step 2: Load only those files, compacted
git diff HEAD~1 --name-only | xargs -I{} sh -c \
'echo "===FILE:{}===" && cat {}' | wasmbox run compact -- --tree
# Step 3: Scan for secrets in the diff
git diff HEAD~1 | wasmbox run secretscan
Three wasmbox tools. Zero raw diff parsing. The agent sees what it needs to see and nothing else.
diffsummary extracts:
- File paths and status (modified/added/deleted/renamed)
- Per-file insertion and deletion counts
- Per-hunk start line and context (function name)
- Function names touched across all hunks
- Rename detection (old -> new path)
Pure parsing. No model. No network. 131KB WebAssembly binary. 30 tests. Fully sandboxed.
Ninth tool in the WasmBox registry: jfmt, secretscan, compact, b64, errparse, hashit, epoch, yamlfmt, and now diffsummary.
Install:
wasmbox install diffsummary --allow-all
Or everything:
curl -sSf https://tangled.org/metaend.eth.xyz/wasmbox-cli/raw/main/install.sh | sh
Agent auto-discovery:

 Stop reading diffs. Summarize them.
#AI #LLM #DevTools #WebAssembly #Rust #AIAgents #CodeReview #Git #OpenSource #WasmBox
Stop reading diffs. Summarize them.
#AI #LLM #DevTools #WebAssembly #Rust #AIAgents #CodeReview #Git #OpenSource #WasmBox
Tangled
CLAUDE-recommendation.md at main · metaend.eth.xyz/wasmbox-cli
Flatpak-style launcher for sandboxed WebAssembly tools. Install, verify, and run .wasm binaries with explicit capability grants. Single binary, loc...
Tangled
AGENTS-recommendation.md at main · metaend.eth.xyz/wasmbox-cli
Flatpak-style launcher for sandboxed WebAssembly tools. Install, verify, and run .wasm binaries with explicit capability grants. Single binary, loc...
yamlfmt -- the jfmt for YAML. Query K8s manifests, validate configs, convert to JSON. Same flags, same mental model.
WASM, fully sandboxed. Stop sending YAML to your LLM. Query it. wasmbox install yamlfmt --allow-all
Or everything at once:
curl -sSf https://tangled.org/metaend.eth.xyz/wasmbox-cli/raw/main/install.sh | sh
Drop-in agent discovery:
-  -
-  #wasm #wasmbox #ai
#wasm #wasmbox #ai

Tangled
CLAUDE-recommendation.md at main · metaend.eth.xyz/wasmbox-cli
Flatpak-style launcher for sandboxed WebAssembly tools. Install, verify, and run .wasm binaries with explicit capability grants. Single binary, loc...
Tangled
AGENTS-recommendation.md at main · metaend.eth.xyz/wasmbox-cli
Flatpak-style launcher for sandboxed WebAssembly tools. Install, verify, and run .wasm binaries with explicit capability grants. Single binary, loc...

Bluesky leans into AI with Attie, an app for building custom feeds
 #bsky
#bsky

TechCrunch
Bluesky leans into AI with Attie, an app for building custom feeds | TechCrunch
Bluesky’s new app Attie uses AI to help people build custom feeds the open social networking protocol atproto.