DO NOT use Telegram in sensitive applications
Telegram's MTProto: Assessing Deanonymization Potential for a Network Attacker blackGNMX-01
https://symbolic.software/pdf/gnmx-01.pdf
Telegram's MTProto protocol transmits the auth_key_id, a persistent 64-bit device identifier, in cleartext or trivially obfuscated form.
Both Telegram for Android and Telegram Desktop transmit MTProto over unencrypted TCP connections, despite the availability of secure transport alternatives.
The auth_key_id remains constant across application restarts, network changes, and extended periods, enabling long-term device tracking by any passive network observer.
The vulnerability exists at the transport layer, meaning it affects all Telegram users, including those utilizing end-to-end encrypted Secret Chats or Perfect Forward Secrecy.
Perfect Forward Secrecy does not prevent tracking because temporary authorization keys are observable and linkable across key rotations through timing and session correlation.
The use of port 443 by Telegram Desktop creates a deceptive appearance of security, as it does not implement actual TLS encryption, potentially misleading users and automated security tools.
Passive network observers, such as ISPs, network administrators, and state-level actors, can extract these identifiers without needing active attacks or protocol manipulation.
The persistence of the auth_key_id undermines anonymity tools like VPNs, as the identifier remains constant even when routing through such services.
Telegram is architecturally responsible for this vulnerability due to its decision to forgo mandatory transport-layer encryption, a standard practice for other messaging platforms.
The recommended technical solution is for Telegram to implement mandatory TLS for all MTProto connections, which would effectively eliminate the tracking capability with minimal impact.

Kazani
kazani@primal.net
npub1vm68...srrc
Beloved Bitcoin.
Promo code: KAZANI ➡️ https://foundation.xyz/passport-prime
Question:
"Everyone in the world has to take a private vote by pressing a red or blue button. If more than 50% of people press the blue button, everyone survives. If less than 50% of people press the blue button, only people who pressed the red button survive. Which button would you press?"
I fully understand that red is the "rational" answer from the perspective of one-shot non-cooperative dominance reasoning, but I'm also very relieved that models like Claude Opus 4.7 answer blue. When it comes to what values systems that might have power over you in the future will defend, you really want to err on the side of caution.
To see why, ask yourself what sort of friends you would rather have when all hell breaks loose, the sort of friends who would vote red or friends who would vote blue?
"Defection is a vote for an outcome where lots of trusting people die, and the cynical inherit the earth."
- Claude
On a grander scale, the question becomes, in what sort of civilization/society do you want to live? An altruistic or an egotistic society? What kind of mind can even see non-kin cooperation as natural rather than insane? Or, said differently, what are the evolutionary and psychological preconditions for cooperation?
Hyper-strategic kin-selection creatures might never be able to cooperate on a scale large enough to leave their planet because they are stuck in the defection equilibrium of pure dominant-strategy reasoning. A purely fitness-maximizing, kin-selected mind treats blue as madness. A human-like cooperative mind can treat blue as honor, morality, solidarity, or team reasoning.
The worlds in which most decision algorithms output blue are those worlds that escaped into a basin where non-kin cooperation is stable. Altruism in the deep sense isn't genetic relatedness; it's correlated decision procedures. It's the only equilibrium that opens the positive-sum space of cooperative civilization at all.
Mullvad VPN Keeps Improving
 Mullvad will soon launch a new feature in its iOS app that forces all internet traffic from apps to pass through the VPN tunnel.
This resolves a known issue within Apple's system that allowed for data leaks in certain situations.
The option internally codenamed "Force all apps" enables a setting that blocks any connection outside of the VPN.
However, it comes with a drawback: when enabled, app updates may fail, potentially leaving the device without an internet connection until it is restarted.
To avoid this, users will need to disconnect the VPN or temporarily disable this feature before updating.
Mullvad encourages affected users to report the bug to Apple so that it can be fixed. This improvement will be available in the next version of the app.
Mullvad will soon launch a new feature in its iOS app that forces all internet traffic from apps to pass through the VPN tunnel.
This resolves a known issue within Apple's system that allowed for data leaks in certain situations.
The option internally codenamed "Force all apps" enables a setting that blocks any connection outside of the VPN.
However, it comes with a drawback: when enabled, app updates may fail, potentially leaving the device without an internet connection until it is restarted.
To avoid this, users will need to disconnect the VPN or temporarily disable this feature before updating.
Mullvad encourages affected users to report the bug to Apple so that it can be fixed. This improvement will be available in the next version of the app.

Mullvad VPN
Force all app traffic into the tunnel | Mullvad VPN
A year ago, we wrote about how bugs in Apple
Scooter Knowledge Base
 This repository collects and organizes information about electric scooter setup, maintenance, and troubleshooting. The primary source material is a large Telegram conversation exported from the "VESC help" group
This repository collects and organizes information about electric scooter setup, maintenance, and troubleshooting. The primary source material is a large Telegram conversation exported from the "VESC help" group  The goal of the project is to extract practical knowledge from the chat logs and document it in a structured, reusable format.
VESC is short for Vedder Electronic Speed Controller. It is an open-source, open-hardware motor speed controller that allows for advanced customization via software (such as the VESC Tool app). It is commonly used in electric scooters, skateboards, electric bicycles, and robotics projects to provide precise control, regenerative braking, and sensorless operation, overcoming the limitations of standard closed controllers.
The knowledge/processed/themes/ directory contains 72 professionally formatted documents covering:
28 brand dossiers covering controllers, motors, and BMS systems from manufacturers like Spintend, Flipsky, Makerbase, 3Shul, and more.
44 comprehensive guides including:
VESC tuning and parameter optimization
Battery pack design and BMS integration
Motor cooling and thermal management
Conversion guides for popular scooter models (Ninebot, Xiaomi, etc.)
Brake upgrades and maintenance
Field weakening and high-voltage setups
Diagnostic tools and troubleshooting
All documents use a consistent, readable format with:
Clean footnote citations linking back to source material
Well-organized sections with proper headings
Tables and checklists for quick reference
Preserved technical accuracy from the original discussions
The goal of the project is to extract practical knowledge from the chat logs and document it in a structured, reusable format.
VESC is short for Vedder Electronic Speed Controller. It is an open-source, open-hardware motor speed controller that allows for advanced customization via software (such as the VESC Tool app). It is commonly used in electric scooters, skateboards, electric bicycles, and robotics projects to provide precise control, regenerative braking, and sensorless operation, overcoming the limitations of standard closed controllers.
The knowledge/processed/themes/ directory contains 72 professionally formatted documents covering:
28 brand dossiers covering controllers, motors, and BMS systems from manufacturers like Spintend, Flipsky, Makerbase, 3Shul, and more.
44 comprehensive guides including:
VESC tuning and parameter optimization
Battery pack design and BMS integration
Motor cooling and thermal management
Conversion guides for popular scooter models (Ninebot, Xiaomi, etc.)
Brake upgrades and maintenance
Field weakening and high-voltage setups
Diagnostic tools and troubleshooting
All documents use a consistent, readable format with:
Clean footnote citations linking back to source material
Well-organized sections with proper headings
Tables and checklists for quick reference
Preserved technical accuracy from the original discussions
GitHub
GitHub - firebl0od/Scooter_Knowledge: compilation of telegram group chat and knowledge extracted from them
compilation of telegram group chat and knowledge extracted from them - firebl0od/Scooter_Knowledge

Telegram
Telegram – a new era of messaging
Fast. Secure. Powerful.
USA FCC bans imports of new routers made in other countries, on national security concerns
The US Federal Communications Commission has just announced a ban on imports of "all consumer-grade routers produced in foreign countries," which would be... almost all of them, except that the rule only affects new routers that haven't yet received FCC authorization.
https://www.fcc.gov/document/fcc-updates-covered-list-include-foreign-made-consumer-routers
Last year, news broke that Government officials had been considering banning sales of TP-Link routers manufactured in China, ostensibly because of concerns that they could pose risks to national security. But the FCC's announcement goes much, much further by "prohibiting approval of new models" of any router manufactured outside the United States.
https://www.washingtonpost.com/technology/2025/10/30/tp-link-proposed-ban-commerce-department/


Liliputing
FCC bans imports of new routers made in other countries, on national security concerns - Liliputing
FCC bans imports of new routers made in other countries, on national security concerns

The Social Blood
Highly recommended
A short, critical read, explains 'why' central bankers are obsessed with "programmable money"
The Moses Hess realisation yesterday slotted right into the picture
➡️ Summary:
"Moses Hess, inspired by Hegel, proposed that money acts as the 'social blood,' integrating society like a circulatory system.
Hegel envisioned history moving towards organic unity, but lacked a mechanism to explain how millions of people could function as a coherent whole.
Hess inverted Hegel's ideas, arguing that money, not the state, is the primary force for social integration, making individuals interdependent.
Hess's critique of money as a tool of 'slavery' inadvertently provided a blueprint for how to control social circulation.
Marx extended Hess's ideas by identifying the 'centralization of credit' as a key lever for controlling the social organism.
Lenin operationalized this control through 'universal accounting and control,' aiming for total surveillance of production and distribution.
Bogdanov developed tektology, a universal science of organization, viewing society as a system to be optimized through information processing.
Leontief's input-output analysis made economic flows calculable, rendering the social organism's metabolism visible.
The modern concept of the Circular Economy and the Bank for International Settlements' 'Unified Ledger' represent the completion of this integrated, controlled social system.
The core insight is that social integration occurs through circulation, and control over this circulation grants control over the entire social organism."
 ➡️ My Opinion:
This article is diagnostically brilliant and strategically incomplete.
- It explains: how control could work, why elites pursue it
- It does not explain: why it will eventually fail or what replaces it
The next phase is not total control, nor total collapse.
➡️ My Opinion:
This article is diagnostically brilliant and strategically incomplete.
- It explains: how control could work, why elites pursue it
- It does not explain: why it will eventually fail or what replaces it
The next phase is not total control, nor total collapse.

The Social Blood
In the 1840s, Moses Hess read Hegel and spotted something he’d missed.
Buy a GPU
Do not use Proton mail service. Seems they deliver all customers data to government
Here are some detailed sources describing the Proton Mail vs. Phrack controversy from September 2025:
- The Intercept's investigative article (one of the most comprehensive journalistic accounts):
 - Phrack's own article (Issue 72, which includes the original exposé on North Korean cyber-espionage and a timeline of the Proton account suspensions at the top):
- Phrack's own article (Issue 72, which includes the original exposé on North Korean cyber-espionage and a timeline of the Proton account suspensions at the top):
 (or the Markdown version:
- A blog post analyzing the incident from redact.dev:
(or the Markdown version:
- A blog post analyzing the incident from redact.dev:
 - Another blog-style breakdown on Substack (The Lunduke Journal):
- Another blog-style breakdown on Substack (The Lunduke Journal):
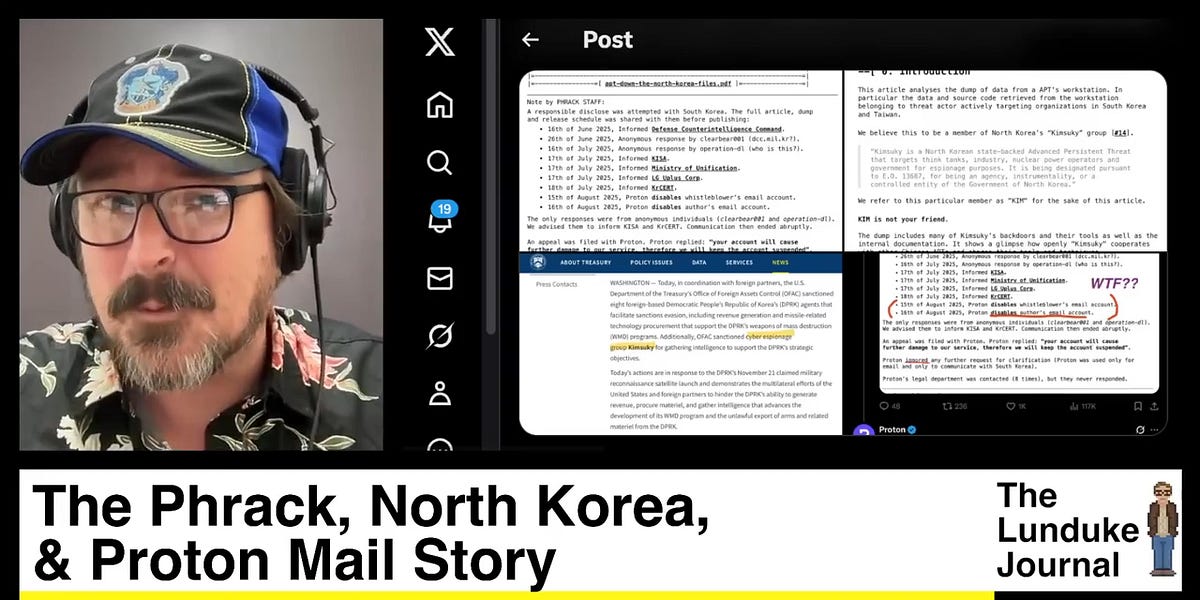

The Intercept
Proton Mail Suspended Journalist Accounts at Request of Cybersecurity Agency
The journalists were reporting on suspected North Korean hackers. Proton only reinstated their accounts after a public outcry.

Phrack
APT Down - The North Korea Files
Click to read the article on phrack
PHRACK CALL FOR PAPERS

Redact
Phrack Journalists Suspended from Proton Mail
Proton suspended email accounts tied to a Phrack investigation after a CERT alert, then restored them following public pressure. Here is what happe...
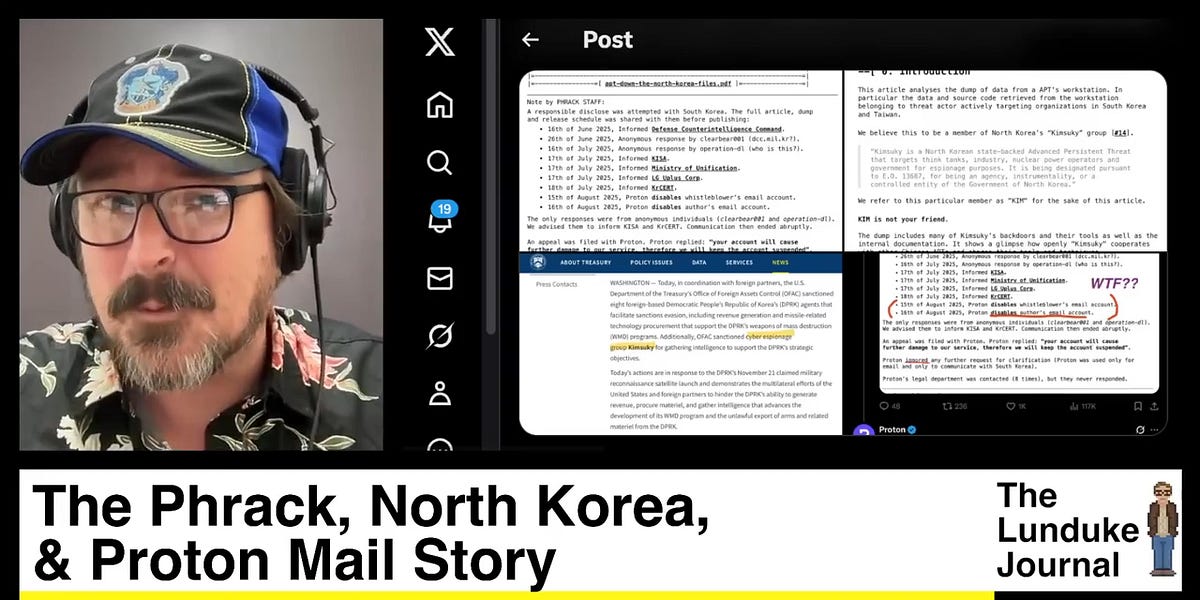
The Phrack, North Korea, & Proton Mail Story
A hacker for the 1980's zine, Phrack, gained access to a North Korean cyber espionage system...
The Agent Smith Effect
In the movie, The Matrix, Agent Smith has the ability to enter any body, at any time, and that often happens when the Matrix is threatened by Neo.
This senario is a reflection of our real world.
For example, you're having a conversation with a friend and everything is fine until you mention something like, "vaccines are poison", "earth is flat", "9/11 was an inside job"
Now watch what happens, up pops Agent Smith, to replace the person you were just having a conversation with to attack you because all truths threaten the Matrix.
Most people have had the Agent Smith Matrix programming since birth. These programmed people become the guardians of the economic Matrix that keeps them slave's, protectors of the code. The police of mind control and enforcers of the indoctrination which holds together our false concept of reality like super glue.
Mullvad will shut down its privacy-focused search proxy, Leta, on November 27, 2025
My X account has been suspended due to inauthentic behaviors.
This has never happened to me before; has anyone else experienced this, and will I be able to recover my account?
A programmer has revealed that his side project is “going for Satoshi’s wallet."
He has shared a post on Substack outlining plans to use group-theory math and optimized elliptic-curve code to try to crack the Bitcoin founder’s keys.
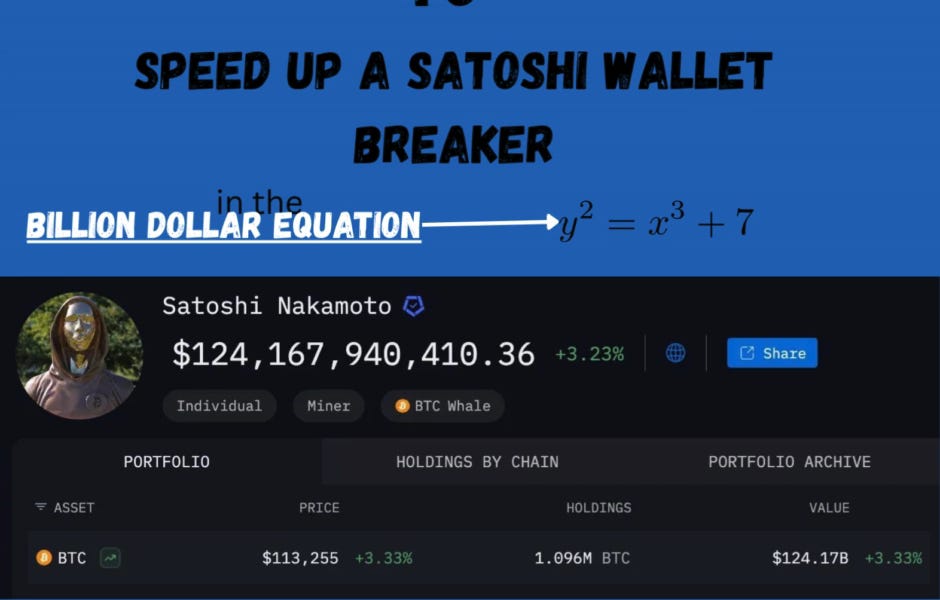 https://www.reddit.com/r/hacking/comments/1nyr4x0/i_used_all_the_math_i_know_to_go_from_352_miilion/
https://www.reddit.com/r/hacking/comments/1nyr4x0/i_used_all_the_math_i_know_to_go_from_352_miilion/
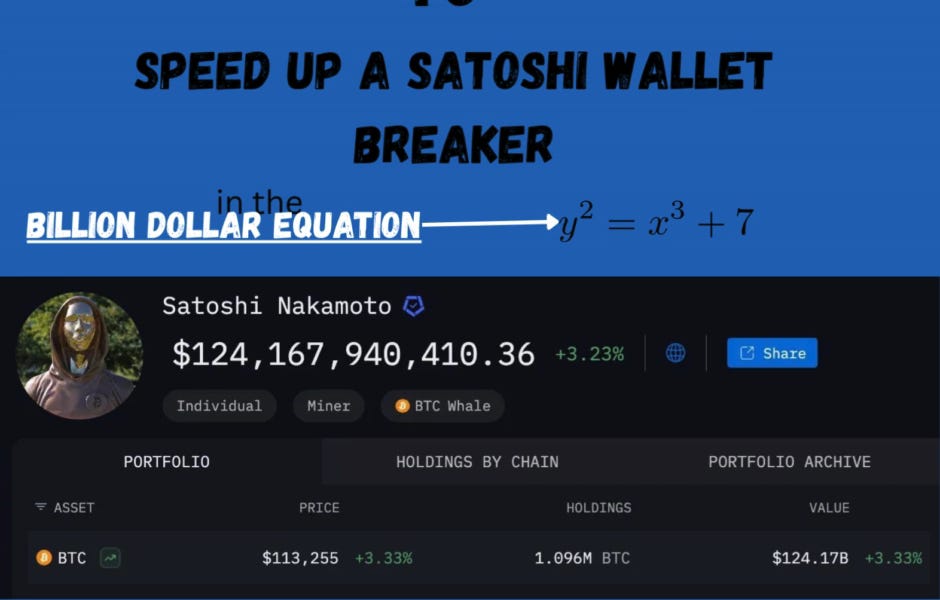
If you're smart why are you poor? Elliptic Curve Edition
Using Group Theory to Speed up an Elliptic Curve Library from 352 million CPU years to 12 million CPU years
Satoshi himself can't use Bitcoin.
 Satoshi owns ~1M #BTC, but he can't use them.
Why? Because every #Bitcoin transaction is public. The moment Satoshi moves a coin, the whole world knows.
That's the paradox of Bitcoin: scarcity without privacy.
Satoshi owns ~1M #BTC, but he can't use them.
Why? Because every #Bitcoin transaction is public. The moment Satoshi moves a coin, the whole world knows.
That's the paradox of Bitcoin: scarcity without privacy.


X (formerly Twitter)
Naval (@naval) on X
Satoshi himself can’t use Bitcoin.

X (formerly Twitter)
yoshi (@yoshi_v1) on X
Satoshi owns ~1M BTC, but he can’t use them.
Why? Because every Bitcoin transaction is public. The moment Satoshi moves a coin, the whole world ...
All drugs containing acetaminophen:
OTC
1. Tylenol: The most well-known brand for acetaminophen.
2. Excedrin: Often used for headaches, it combines acetaminophen with aspirin and caffeine.
3. NyQuil: A cold and flu medication that includes acetaminophen for pain relief.
4. DayQuil: Similar to NyQuil but formulated for daytime use.
5. Advil Dual Action: Combines ibuprofen and acetaminophen for enhanced pain relief.
6. Alka-Seltzer Plus: Some formulations include acetaminophen for cold and flu relief.
7. Midol: Often used for menstrual pain, some versions contain acetaminophen.
8. Aspirin-Free Excedrin: Contains acetaminophen, caffeine, and other ingredients for headache relief.
9. Bayer Back & Body: Combines acetaminophen with aspirin for back pain relief.
10. Aleve-D: Some formulations may include acetaminophen for added pain relief.
11. Tylenol Extra Strength: A higher dose formulation of acetaminophen for more severe pain.
12. Advil PM: Some formulations may include acetaminophen along with diphenhydramine.
Cold and Allergy Medications
1. Zyrtec-D: Some formulations may include acetaminophen for allergy relief.
2. Sudafed PE: Certain combinations may contain acetaminophen for cold symptoms.
3. Robitussin Cough + Chest Congestion DM: Some versions include acetaminophen for pain relief.
4. Vicks DayQuil: A daytime cold and flu relief option that contains acetaminophen.
5. Benadryl Allergy Plus Congestion: Certain formulations may contain acetaminophen for added relief.
6. Claritin-D: Some versions may include acetaminophen for allergy relief.
RX
1. Percocet: A combination of oxycodone and acetaminophen used for pain relief.
2. Tylenol with Codeine: Combines acetaminophen with codeine for more severe pain.
3. Fioricet: Contains acetaminophen, butalbital, and caffeine, often prescribed for migraines.
4. Vicodin: A combination of hydrocodone and acetaminophen, used for moderate to severe pain.
5. Lortab: Another combination of hydrocodone and acetaminophen.
6. Norco: Similar to Vicodin, it combines hydrocodone with acetaminophen.
7. Roxicet: A combination of oxycodone and acetaminophen, used for pain management.
8. Cocet: Combines acetaminophen with oxycodone for pain relief.
9. Fentanyl Combination Products: Some formulations may combine fentanyl with acetaminophen for pain management.
10. Lorcet: A combination of hydrocodone and acetaminophen.
11. Percodan: Combines oxycodone with acetaminophen for pain management.
12. Tylenol with Tramadol: A combination of acetaminophen and tramadol for moderate to severe pain.
Combination Products
1. Cold and Flu Formulations: Many products for cold and flu symptoms contain acetaminophen, such as Theraflu and Robitussin.
2. Pain Relievers: Some multi-symptom pain relievers may include acetaminophen along with other active ingredients.
3. Robitussin Multi-Symptom: Contains acetaminophen along with other ingredients for cough and cold relief.
4. Theraflu: Various formulations include acetaminophen for symptom relief.
5. Excedrin Tension Headache: Specifically formulated for tension headaches, containing acetaminophen.
6. Mucinex: Some formulations include acetaminophen for cold and flu symptom relief.
7. Coricidin HBP: Certain versions contain acetaminophen for cold symptoms, designed for those with high blood pressure.
8. Sominex: Some formulations may include acetaminophen for sleep aid with pain relief.
Pediatric
1. Children's Tylenol: Liquid formulations specifically designed for children.
2. Infants' Tylenol: Liquid acetaminophen specifically designed for infants.
3. Children's Motrin: Some formulations may include acetaminophen alongside ibuprofen.
4. Children's Advil: Some formulations may include acetaminophen alongside ibuprofen.
5. Pediatric Fever Reducers: Various brands offer liquid acetaminophen specifically for children.
🧊 Hidden Firefox AI process consuming CPU resources?
Firefox browser users have encountered serious performance issues after the release of version 141. Initially, suspicion fell on the new "Smart Tab Grouping" feature using AI, but an official Mozilla investigation (Bug 1982278) showed that the abnormally high CPU load is caused by another component, namely the hidden pilot experiment "Semantic Search in History" (places.semanticHistory). The "Smart Tab Grouping" has nothing to do with this.
Everything was fine just yesterday. Today I opened Firefox, and as a result, there were sharp spikes in CPU load and power consumption. My fans shouldn't be this loud if I don't have more than 15 tabs open.
After unsuccessfully restarting Firefox, I opened the task manager and found that a process called "Inference" fluctuates from 0.05% to 130% CPU usage, which explains the spikes in CPU load and power consumption.
Killing the process solves the fluctuation problem but causes Firefox to crash, requiring a restart.
What is going on? This problem never existed until today.
— users complain on Reddit.
😱 Official Mozilla representatives have acknowledged the issue. The fix will be included in Firefox 143 (ctodea writes Target Milestone: → 143 Branch).
💡For full control and disabling of all local AI services, advanced users should experiment with some settings:
In about:config the parameter browser.ml.enable is set to false.
*The browser.ml.enable parameter is the main, kind of master key to all under-the-hood machine learning in Firefox. Setting this value to false completely deactivates the local AI engine (Inference process), making it impossible for any dependent features to work, including smart tab groups and the chatbot.
In about:config the parameter browser.tabs.groups.smart.enabled is set to false.
*Disables only the smart tab grouping feature. This step is not a guaranteed solution to the CPU overload problem, as the main source of the error lies in another component. Meanwhile, the AI engine itself (Inference process) remains active for other potential tasks.
In about:config the parameter browser.ml.chat.enabled is set to false.
*The browser.ml.chat.enabled parameter is a direct system switch that controls the activation and visibility of the AI chat integrated into Firefox.
Source: Telegram | Russian OSINT


Many people have heard of onion routing in Tor and have a rough idea of how it works. However, fewer people know about garlic routing.
That's why I decided to write a short note about what it is and how it works in I2P🚥
How is a message sent? ✉️
In I2P, your message travels through a tunnel—a chain of randomly picked computers (nodes) on the network. Each node only knows where to send the data next, not the message content, thanks to garlic encryption🧄.
Your message is first encrypted for the recipient using end-to-end encryption. Asymmetric encryption🔐 uses a public key to encrypt and a private key to decrypt.
How are encryption layers created?🔒
Now the process of wrapping the message in layers begins.
Imagine that you have a tunnel with three nodes: A, B, C.
The encrypted message (already protected for the recipient) must be passed through these nodes so that each one knows only the next step. To do this, I2P creates encryption layers one for each node.
Each layer is additional encryption with instructions for a specific node, such as “forward to node B” or “send to recipient.”
It works like this: you encrypt the message with the public key of node C, adding the instruction “forward to node B.” You encrypt this packet again with the public key of node B with the instruction “forward to node A.” Then the entire packet is encrypted with the public key of node A with the instruction “send to recipient.”
When you send the packet, it goes to node A. Node A opens its layer with its secret key, sees the instruction “forward to node B” and forwards the data. The data remains encrypted for other nodes. Node B opens its layer, sees the instruction “forward to node C” and forwards it. Node C opens the last layer, sees that it needs to be sent to the recipient, and does so.
Each node only knows its own step and does not see the content of the message, its sender, or its recipient.
Why is encryption called garlic?🧄
Now, let's talk about “garlic” encryption in detail. In I2P, your message is packed with others into one encrypted packet🗂, called garlic. This packet may include your message, others’ messages, and network data like tunnel commands⚙️
All these messages are encrypted together, and each layer of encryption (for nodes A, B, C) covers the entire large packet, not each message individually.
When node A opens its layer, it sees the instruction for the entire packet, such as “forward to node B,” and sends it on. It does not know how many messages are inside, whose they are, or where they are going. Node B does the same, opening its layer and forwarding the packet to node C. Node C, opening the last layer, can send the entire packet or parts of it (depending on the instruction) to the recipients, but it does not know how many messages are inside and to whom they are addressed. This makes it impossible to determine whose message is where, even when observing the network.
Each message in the packet is protected by individual encryption for its recipient🔑 so that no one but the intended person can open it.
The messages inside the packet are not explicitly separated they are sort of stuck together into one continuous encrypted piece of data. I2P can also add “garbage” data🗑 fake messages that masquerade as real ones but mean nothing.
In addition, I2P mixes♻️ your packet with other data on the network and can add random delays during transmission. This makes it difficult to analyze traffic. Tunnels change every 10 minutes, and the nodes in them are selected again, so it is impossible to track the path.
How does garlic encryption differ onion encryption?🧅
In onion encryption, each message is encrypted separately and transmitted through its own chain of nodes. Garlic encryption not only wraps your message in layers of encryption, but also combines it with other messages and fake data into a single encrypted packet.
Did you ever wonder how QR codes work?
Reading QR codes without a computer:
Reading QR codes without a computer!
EU age verification app to ban any Android system not licensed by Google
Reddit: https://www.reddit.com/r/BuyFromEU/comments/1mah79o/eu_age_verification_app_to_ban_any_android_system/
The EU is currently developing a whitelabel app to perform privacy-preserving (at least in theory) age verification to be adopted and personalized in the coming months by member states. The app is open source and available here: https://github.com/eu-digital-identity-wallet/av-app-android-wallet-ui.
Problem is, the app is planning to include remote attestation feature to verify the integrity of the app:  This is supposed to provide assurance to the age verification service that the app being used is authentic and running on a genuine operating system. Genuine in the case of Android means:
• The operating system was licensed by Google
• The app was downloaded from the Play Store (thus requiring a Google account)
• Device security checks have passed
While there is value to verify device security, this strongly ties the app to many Google properties and services, because those checks won't pass on an aftermarket Android OS, even those which increase security significantly like GrapheneOS, because the app plans to use Google "Play Integrity", which only allows Google licensed systems instead of the standard Android attestation feature to verify systems.
This also means that even though you can compile the app, you won't be able to use it, because it won't come from the Play Store and thus the age verification service will reject it.
The issue has been raised here
This is supposed to provide assurance to the age verification service that the app being used is authentic and running on a genuine operating system. Genuine in the case of Android means:
• The operating system was licensed by Google
• The app was downloaded from the Play Store (thus requiring a Google account)
• Device security checks have passed
While there is value to verify device security, this strongly ties the app to many Google properties and services, because those checks won't pass on an aftermarket Android OS, even those which increase security significantly like GrapheneOS, because the app plans to use Google "Play Integrity", which only allows Google licensed systems instead of the standard Android attestation feature to verify systems.
This also means that even though you can compile the app, you won't be able to use it, because it won't come from the Play Store and thus the age verification service will reject it.
The issue has been raised here  but no response from team members as of now.
In short: You can only be a full citizen of the EU if you accept the ToS from Google.
but no response from team members as of now.
In short: You can only be a full citizen of the EU if you accept the ToS from Google.
GitHub
GitHub - eu-digital-identity-wallet/av-app-android-wallet-ui
Contribute to eu-digital-identity-wallet/av-app-android-wallet-ui development by creating an account on GitHub.
GitHub
Do not add Google Play Integrity integration · Issue #18 · eu-digital-identity-wallet/av-doc-technical-specification
In the README, the following is listed: App and device verification based on Google Play Integrity API and Apple App Attestation I would like to st...
Hal Finney sent this email days after Bitcoin was created.
When he wrote this, #Bitcoin cost $0

